IoT devices or ‘things’ are internet-connected devices that collect, transmit, and receive information. They vary from simple sensors to complex systems, including smart homes, industrial control systems, and medical devices. IoT devices are used in different industries, like healthcare, manufacturing, transportation, and smart cities. Examples of IoT devices include security cameras, wearable devices, and autonomous vehicles, which are often deployed in sensitive industries and require robust security measures.
The increasing number of IoT devices also increases the possibilities of cyber-attacks, and therefore better security mechanisms/implementations are required for safety. Most IoT devices have multiple features and open ports, which can increase their vulnerability to attacks. The growing number of networked devices introduces new IoT security challenges and IoT security issues that organizations must address. Cyber threats are a significant concern for IoT environments. It is crucial to protect sensitive data, ensure data integrity, and use data encryption to secure IoT communications and storage. Managing access and user access to IoT devices, along with implementing secure authentication and robust identity credentials, is essential for preventing unauthorized access. Organizations must also consider supply chain security and regulatory requirements when deploying IoT devices. IAM in IoT security ensures that sensitive information and resources can be accessed by authorized individuals and devices.
Introduction to IoT Security
The Internet of Things (IoT) is transforming the way we live and work by connecting physical devices, vehicles, home appliances, and countless other items through embedded sensors, software, and network connectivity. This vast ecosystem of connected devices enables seamless data collection and exchange, driving innovation across industries. However, as the number of IoT devices grows, so does the need for robust IoT security. Protecting the confidentiality, integrity, and availability of sensitive data transmitted between devices is a critical component of any IoT deployment. Implementing robust authentication mechanisms and comprehensive access management systems is essential to prevent unauthorized access and data breaches. Identity management systems play a vital role in managing digital identities and controlling access, ensuring that only authorized users and devices can interact with sensitive systems. As organizations continue to expand their use of IoT technology, prioritizing security is key to safeguarding devices, data, and the overall integrity of the internet of things (IoT) ecosystem.
Why is IAM necessary in IOT?
The process of identifying, authenticating, and granting access to resources based on either the device or user identity is known as identity and access management (IAM) in IoT devices. The process starts by identifying the device or user with something unique, like a product serial number or a username. The next stage is authentication. The process of confirming a device’s or user’s identity by requesting credentials, such as a password or a digital certificate, is known as authentication.
Users and devices may have multiple identities across different platforms, applications, or systems, and IAM helps reconcile these identities to provide a comprehensive view and appropriate access control. Alternatively, IAM can manage a single identity for each user or device to streamline authentication and authorization across environments.
IAM is a set of policies, practices, and guidelines that a business applies to manage digital identities and control resource access. IoT IAM includes controlling user and device identities and ensuring that only people with the necessary permissions can access or interact with the network.
IAM systems often need to integrate with multiple systems to ensure seamless access, provisioning, and de-provisioning across complex environments. Organizations deploy IAM solutions to manage device onboarding, including the use of temporary credentials for secure initial authentication before assigning permanent identities. IAM is critical for preventing unauthorized access and ensuring that only the right people can access sensitive resources. It must also address physical access to devices, as attackers with physical access can steal data or compromise device security. Additionally, IAM must consider the underlying operating systems of IoT devices, since these can impact identity management and the overall security posture.
Threats to IoT Devices
IoT devices face a wide range of security threats that can compromise sensitive data and disrupt operations. Cyber criminals often exploit software vulnerabilities, weak or default passwords, and unsecured networks to gain access to many IoT devices. Once inside, attackers can steal sensitive data, manipulate device behavior, or use compromised devices to launch large-scale distributed denial-of-service (DDoS) attacks, increasing the risk of data breaches and network outages. The rapid proliferation of IoT connections expands the attack surface, making it easier for cyber attacks to target multiple devices simultaneously. To address these challenges, organizations must prioritize IoT security by implementing robust authentication mechanisms, such as multi-factor authentication, and ensuring that all devices are properly configured and regularly monitored. By proactively addressing these threats, organizations can significantly reduce the risk of unauthorized access and protect their IoT infrastructure from malicious activity.
Role of IAM in Securing IoT Devices
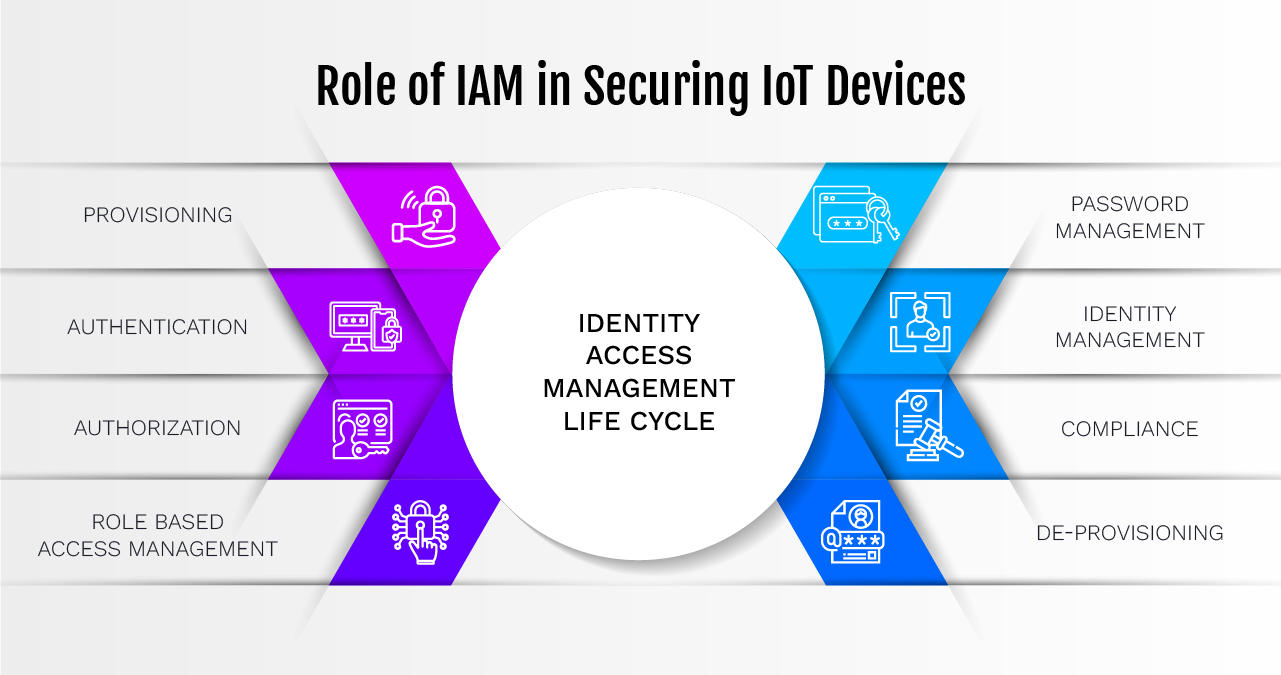
Figure 1: IAM Life Cycle
1. Device Authentication: IoT devices can be authenticated by IAM systems prior to gaining network access. This means confirming the identity of each device to allow only the ones that have permission. Methods include using certificates, passwords, or cryptographic keys. Secure authentication and robust identity credentials are essential for establishing trust and ensuring only secure IoT devices are allowed to connect.
2. Access Control: IAM solutions control the resources and data that a device can access after it has been authenticated. Device capabilities can be restricted according to specified policies using either role-based access control (RBAC) or attribute-based access control (ABAC). For example, a thermostat may only be able to change the temperature; it may not be able to access other network resources.
3. User Management: User identities and their interactions with IoT devices are managed by IAM systems. To illustrate a practical application of IAM for IoT, if a user must perform an action on an IoT device through a mobile application, the IAM will make certain the user has been authenticated and given the authorization to perform that specific action. Managing user access and effectively managing access rights are critical to maintaining security and privacy.
4. Policy Enforcement: IAM platforms enforce security policies (e.g., encryption and data management protocols) throughout the entire IoT infrastructure by requiring compliance with the organization’s security standards. Enforcing security requirements and implementing an additional layer of security, such as in zero trust frameworks, further strengthens device authentication and threat mitigation.
5. Audit and Monitoring: IAM supplies an audit and monitoring capability that permits organizations to determine how their end-user devices and data interact with each other. They keep track of all requests for access, all attempts to authenticate (both successful and unsuccessful), and all activity taking place on devices. IAM also allows an organization to comply with governmental regulations and react to security incidents. Tracking device provenance and the supply chain is important to ensure device authenticity and security.
6. Lifecycle Management: IAM solutions address the ongoing management of IoT devices. IAM provides for the onboarding of devices; IAM enables the modification of access rights/disabling access rights to devices; when the devices are either retired or replaced, IAM allows for their secure decommissioning. Keeping IoT firmware updated is crucial to address vulnerabilities and maintain device security.
7. Mitigating Insider Threats: IAM helps reduce the likelihood of present-day threats from within the organization where the authorized personnel may attempt to misuse their credentials to create an insider threat.
Data Protection
Data protection is a cornerstone of effective IoT security, as connected devices routinely transmit and store sensitive information that must be safeguarded from unauthorized access. To protect this data, organizations should implement strong encryption protocols, ensuring that all data exchanged between IoT devices and networks remains confidential and secure. Access management systems are essential for controlling who can access sensitive data and under what circumstances, helping to prevent data breaches and unauthorized disclosures. It is also crucial to properly configure all IoT devices, including changing default passwords and disabling unnecessary services, to minimize vulnerabilities. By prioritizing data protection and leveraging access management solutions, organizations can protect user identities, maintain the integrity of sensitive information, and build trust with customers and stakeholders.
Cloud-Based Security Solutions
Cloud-based security solutions have emerged as a powerful tool for securing IoT devices and networks. These solutions offer real-time monitoring, advanced threat detection, and rapid incident response, enabling organizations to quickly identify and address security threats as they arise. Leveraging the scalability and flexibility of the cloud, organizations can deploy analytics and machine learning capabilities to gain deeper insights into device behavior and detect potential security risks before they escalate. Cloud-based platforms also streamline security operations by automating software updates, patch management, and vulnerability assessments, ensuring that all IoT devices remain secure and up-to-date. By adopting cloud-based security solutions, organizations can simplify the process of securing IoT devices, reduce operational costs, and enhance their overall security posture in an increasingly connected world.
IAM’s Contribution to the Security of IoT
- Establishing robust Identity and Access Management processes is a required approach to IoT device security. Recommended practices to consider are as follows:
- Implement Strong Authentication: Employ sophisticated authentication methods, such as digital certificates or biometrics, to verify the identity of both IoT devices and users. Use data encryption to protect sensitive data during authentication processes and ensure data integrity throughout device communications.
- Setup Access Controls: Design and implement various policies that restrict access to sensitive information and resources based on user role, location, and time.
- Maintain System Updates: Upgrade firmware and software on a regular basis to guard against known vulnerabilities and security risks. Regular updates help address IoT security issues and challenges, including the risk of cyber threats targeting device vulnerabilities.
- Tracking and Documenting Activity: Monitor and document IoT device and resource access to help detect and prevent suspicious or illegal activity. Monitoring should also include attempts to steal data, ensuring early detection of potential breaches.
- Educate Users: Be informed on the importance of Identity Access Management (IAM) and how to effectively manage their Identity and Access Management.
- Multi -factor Authentication: IoT devices can have Multi-factor Authentication (MFA) interoperability options that allow users to utilize their password and a technique based on their physical characteristics or an external token in conjunction to interact with IoT devices.
- Implement a security model that uses Zero-Trust principles, where no devices are trusted by default. Always validate the device IDs and provide access to the least number of privileges necessary by ensuring that only authorized and approved resources can communicate with the IoT device. During device onboarding, use temporary credentials to establish trust before assigning permanent identities.
IAM Business Trends for IoT
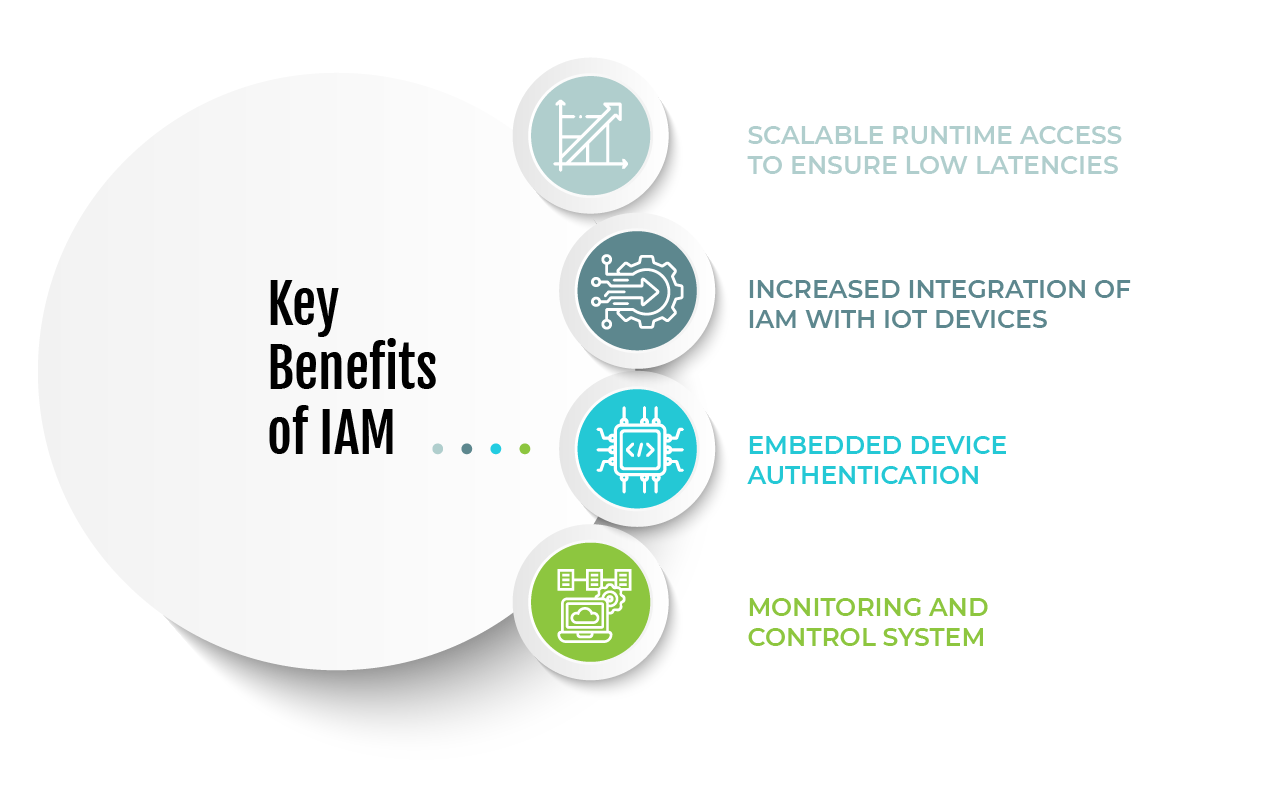
Figure 2: Key benefits of IAM
To keep up with the growing number of IoT devices, companies should provide a way to access them on-demand with as little delay as possible, which means that the data must be stored efficiently and both structured and unstructured data will need to be managed effectively to ensure that the data can be transmitted as quickly as possible, while ensuring that they help support the goals of the IoT platform. Managing multiple identities across multiple systems presents a significant challenge, as individuals and entities often possess several distinct identities across different platforms and applications. Consolidating these into a single identity simplifies access control, improves security, and reduces administrative overhead, while integrating IAM across multiple systems ensures seamless provisioning and de-provisioning in complex environments. There is an increasing trend among IoT suppliers to embed IAM technology into their IoT solutions to create a simplified security solution for customers and help protect their data. Collaborating with authentication experts is helping to fill current authentication solution gaps; however, there is still a long way to go before the Internet of Things (IoT) industry achieves a set of commonly accepted, industry-wide authentication standards.
Many IoT devices come with default passwords, which are often not changed by the user or are changed incorrectly and leave the device vulnerable. Laws such as California’s Consumer Privacy Protection Act require that devices use unique encrypted passwords, yet if these passwords are widely available, the risk will still exist. Providing additional security will also help resolve this issue. As the IoT continues to develop, the need to effectively manage user identities across different systems will grow, and IAM solutions will play a critical role in this. Meeting regulatory requirements and ensuring supply chain security are also becoming increasingly important in IoT business trends, as compliance and device provenance are essential for maintaining trust and integrity. Additionally, as IoT adoption grows, organizations must prioritize efforts to protect sensitive data, such as medical records and intellectual property, from cyber threats and breaches. Users accessing data through stolen or shared passwords continues to be a common issue, especially when employees share login credentials without realizing it.
Conclusion
As it offers strong methods for identification, authorization, and access control, Identity and Access Management (IAM) is essential to the security of Internet of Things devices. As organizations continue to embrace the power of IoT devices, their dependence on this technology will only increase. Implementing strong authentication methods, enforcing granular access policies, as well as providing continued monitoring and updating of security practices through IAM provides organizations with protection against unauthorized users gaining access to IoT networks and/or exposing the networks to compromise. Having a unified IAM strategy in place for the entire ecosystem of IoT devices/systems will also help ensure that only those individuals/devices that are validated and/ or authenticated can access sensitive data within the organization, thus maintaining the integrity/security of the data and protecting the organization from a potential liability.
Organizations in all vertical and market sectors will require the use of IoT devices to improve their business processes; therefore, they need to implement a robust, comprehensive set of security protocols to establish an appropriate level of security risk management for their connected devices. This will reduce the likelihood of a security breach.
eInfochips has been in the business of providing comprehensive digital security solutions around the world for quite some time now. Our team’s extensive experience and expertise have allowed us to develop a comprehensive portfolio of cybersecurity services, including end-to-end device network security, and covering every layer of the connected device ecosystem – device connection, application, and beyond through our strategic, transformative, and managed services approach. This enables us to deploy complete cybersecurity capabilities quickly and easily to customers within their connected device networks.











