The Bluetooth wireless communication protocol is commonly used by smartphones, computers, headphones, and Internet of Things (IoT) devices to exchange data over short distances. However, these attacks pose a threat to the security of IoT devices that utilize Bluetooth technology.
Various Bluetooth Versions
Bluetooth 5.3 (2021)
An incremental upgrade, Version 5.3 adds more stability, security, and efficiency. Peripherals can list preferred channels with a central device.
Bluetooth 5.2 (2020)
Peer devices can request variable power from LE power control (LEPC), which is available. Parallel actions between LE clients and servers are made possible by the enhanced attribute protocol (EATT).
Bluetooth 5.1 (2019)
The tracking accuracy increases with the number of antennas, and the generic attribute (GATT) profile caching reduces the amount of retraining needed to link devices.
Bluetooth 4.1 (2013)
Increased data interchange effectiveness and improved LTE frequency coexistence. Bluetooth devices can interact with one another thanks to BT 4.1’s ability to sustain connections with less user intervention and the simultaneous use of devices as clients and hubs. In the days before Bluetooth 4.1, devices broadcast to a hub via a standalone dongle or a built-in hub.
Bluetooth 3 + HS (2009)
It was advertised as Bluetooth 3.0 + HS (High Speed), and although the connection was established over Bluetooth, the data was sent over Wi-Fi.
Bluetooth 2.1 (2007)
To improve pairing and speed, Secure Simple Pairing (SSP) was implemented. Security was enhanced, encryption was made necessary, and power consumption decreased.
Every Bluetooth version has security holes. Versions 2.1 and 3.0 are extremely vulnerable to assault. For example, these versions do not offer Man-in-the-Middle (MITM) security when pairing.
The following Bluetooth exploits can target Internet of Things (IoT) devices
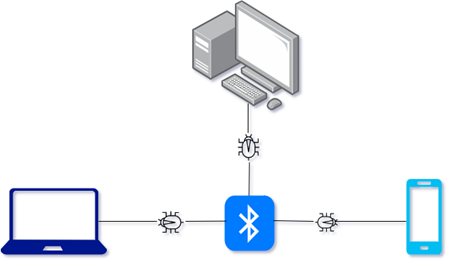
- Blue Borne: Many Internet of Things (IoT) devices with Bluetooth capabilities are vulnerable to a series of BlueBorne flaws. Due to these vulnerabilities, an attacker can take over the target device, run arbitrary code, and infect other Bluetooth-enabled devices with malware.
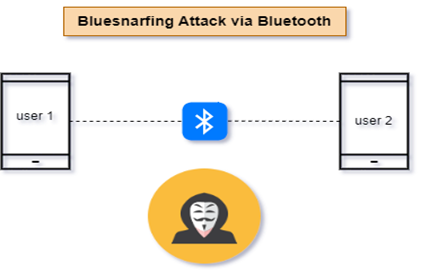
- Bluetooth spoofing: To connect with a target IoT device, Bluetooth spoofing involves pretending to be a real Bluetooth device. Once the connection is made, the attacker can engage in several destructive actions, such as stealing confidential information or inserting malicious instructions.
- Bluetooth Eavesdropping: If the transmission is not properly protected, an attacker within Bluetooth range can intercept and eavesdrop on data transferred between IoT devices and Bluetooth-enabled devices. This could lead to the exposure of sensitive data.
- BlueSmack: Targeting Bluetooth-enabled devices, BlueSmack is a denial-of-service (DoS) attack that bombards them with many malicious Bluetooth packets. The targeted IoT devices may crash or stop responding because of this attack, which will interfere with how they normally function.
- Bluetooth Sniffing: Bluetooth sniffing is the process of recording and examining Bluetooth signals among devices. Attackers can employ specialized tools to intercept Bluetooth communication and collect sensitive data, such as encryption keys or login passwords, to be used in subsequent attacks.
Recent Bluetooth Attack:
Ohio State University researchers identified the exploit known as Bluetooth Address Tracking (BAT) in 2022. By taking advantage of a Bluetooth protocol design fault, it enables attackers to locate Bluetooth devices.
Attacks against Bluetooth-enabled devices that track and monitor them without their consent by taking advantage of their distinctive Bluetooth MAC addresses are known as Bluetooth address tracking attacks, Bluetooth tracking, or Bluetooth device fingerprinting. By observing the existence and usage of Bluetooth devices, these assaults seek to learn about people’s whereabouts and behavioral patterns. In these kinds of attacks, the attacker can passively search for Bluetooth signals broadcast by nearby devices. When a Bluetooth device is discoverable or actively looking for connections, its MAC address is broadcast to other Bluetooth devices. An attacker can develop a profile of a person’s movements and activities by collecting these MAC addresses over time and connecting them to certain places or events.
Attackers can trace the whereabouts of Bluetooth devices using a technique known as Bluetooth Address Tracking. It operates by taking advantage of a Bluetooth protocol design fault that lets attackers determine a Bluetooth device’s allowlist. The list of devices on the allowlist is those that can connect to a Bluetooth device. Attackers can locate a Bluetooth device by discovering the allowlist and then tracing the devices that are permitted to connect to it.
Ohio State University researchers made the initial discovery of the BAT attack in 2022. They showed that the technique could be used to precisely pinpoint the position of Bluetooth devices. Bluetooth Low Energy (BLE) devices, which are frequently used in fitness trackers, smartwatches, and other wearable technology, are particularly well-tracked by the assault.
Prevention Methods for Bluetooth Attacks:
IoT security services are crucial in preventing Bluetooth attacks by putting in place a variety of safeguards to protect IoT devices and the data they transfer via Bluetooth. Some significant security services that can guard against Bluetooth assaults in the context of IoT are listed below:
- Secure Pairing: To ensure that devices create secure and authenticated connections, IoT security services can impose secure pairing protocols like Bluetooth Secure Simple Pairing (SSP) or Bluetooth Low Energy (LE) Secure Connections. This protects against man-in-the-middle attacks and prevents unauthorized pairing.
- Encryption: IoT security solutions can use encryption techniques to protect the integrity and confidentiality of data sent via Bluetooth. They ensure that data transferred between devices is secure and unbreakable by utilizing encryption techniques like AES (Advanced Encryption Standard).
- Authentication and Access Control: Before allowing Bluetooth devices to connect to IoT networks or access confidential information, services can implement robust authentication mechanisms to verify their legitimacy. Techniques that can be employed in this include device certificates, two-factor authentication, and secure key exchange protocols.
- Firmware and software upgrades: IoT security services can assist with managing and distributing firmware and software upgrades for Bluetooth-enabled IoT devices. Regular updates ensure that devices have the most recent security patches and fixes, resolving known vulnerabilities and reducing the risk of Bluetooth-based attacks.
- Intrusion Detection and Prevention: Security services can set up intrusion detection and prevention systems (IDPS), which monitor network traffic and Bluetooth communications for unusual activity or trends. These systems offer an additional line of defense against attacks by being able to identify and deny unauthorized Bluetooth connections, odd behavior, and malicious efforts.
- Penetration testing and vulnerability assessments: IoT security services can frequently perform penetration tests and vulnerability analyses on Bluetooth-enabled IoT devices and the infrastructure that supports them. This aids in identifying potential security gaps and vulnerabilities that attackers might exploit. By conducting security assessments, organizations can proactively fix weaknesses and enhance their overall security posture.
- Threat Intelligence and Monitoring: Security services can make use of threat intelligence resources and use ongoing monitoring to keep current on the most recent Bluetooth-related threats and attack methodologies. This enables them to proactively address new threats and put in place the required security measures.
- Security Awareness and Training: To inform IoT device users, administrators, and developers about Bluetooth security best practices, services can offer security awareness programs and training sessions. This entails encouraging the use of strong passwords, avoiding unauthorized connections, and building a security-conscious culture.
Organizations may improve the security of their Bluetooth-enabled IoT devices, networks, and data by using these IoT security services. It is crucial to work with reputable security service providers who are knowledgeable about the difficulties and needs of safeguarding IoT environments.
IoT security teams should routinely conduct vulnerability analyses to find any potential security flaws in Bluetooth components as well as the firmware or software of IoT devices. They must keep up with the most recent security patches and updates that device makers offer and quickly implement them to prevent known vulnerabilities.
Conclusion
In this blog, we investigated Bluetooth security, covering security features and services. Then, we explored multiple Bluetooth attacks that are mostly brought on by the pairing process. We also delved into Bluetooth risk management, protective measures, and different Bluetooth versions. Currently, both Bluetooth technology and Bluetooth-connected devices are vulnerable to a wide range of security flaws. Users should be aware of the dangers associated with using Bluetooth technology on their devices and the mitigation strategies that may be applied to secure their devices and data from hackers.
From design and certification to production, eInfochips provides a wide variety of test solutions for Bluetooth testing. With testing services that encompass functionality, security, performance, and interoperability, we help businesses swiftly bring their connected devices and products to market. Contact us to learn more about our cybersecurity solutions.
References:
https://home.sophos.com/en-us/security-news/2021/bluetooth-attacks
https://cybersecurity.att.com/blogs/security-essentials/bluetooth-security-risks-explained
https://www.pcmag.com/encyclopedia/term/bluetooth-versions










