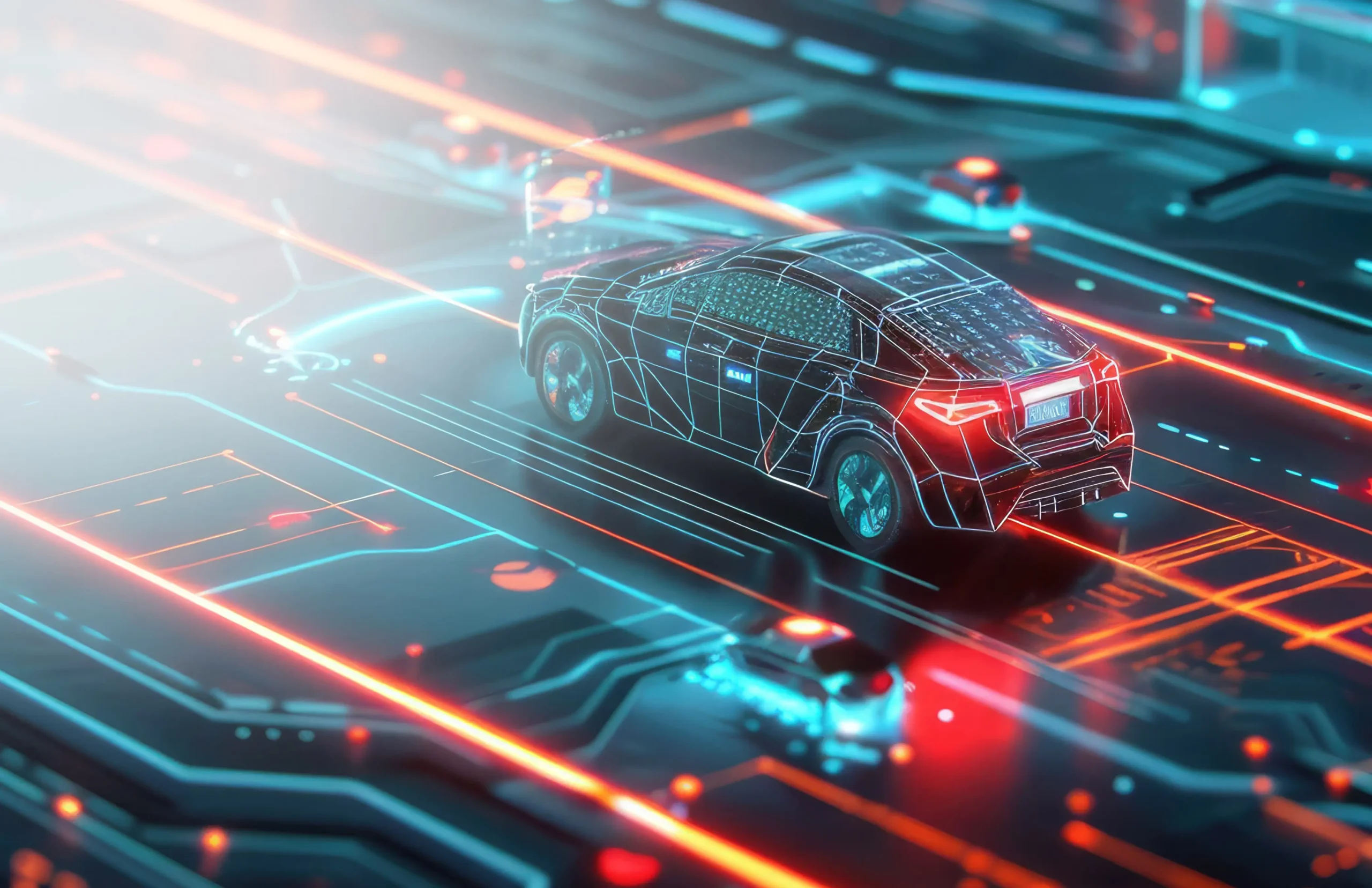
Imagine on a fine day, you enter in your car and see a message on the dashboard to pay a hefty ransom amount to get your car control back. Traditional car attacks were limited to stealing the car by smashing the window. But with technology innovations, new age attacks are more dangerous such as hijacking the car systems and showing the wrong telemetry on the dashboard, taking control of steering, applying the brake at the wrong time, and switching off the engine.
Upstream Security’s report says that automotive cybersecurity attacks have doubled in 2019 from 2018 and increased to 605% since 2016. With this fact, the UN has announced regulations for UNECE countries on automotive cybersecurity for establishing clear performance and audit requirements by January- 2021. So, car manufacturers need to invest in security of connected car ecosystem. McKinsey & Company research says that the automotive cybersecurity market will experience massive investment up to 9.7 billion USD in 2030 from 4.9 billion USD in 2020.
Connected cars IoT spectrum includes multiple components such as Automotive Electronic Control Unit (ECU), Advanced Driver Assistance Systems (ADAS), and V2X communication systems. Let us look at various attack patterns and remedies against each of these components.

Automotive Electronic Control Unit (ECU)
Today’s luxury cars have up to 150 ECUs with 100 million lines of code and researchers say that by 2030, cars would have typically 300 million lines of code. This shows the complexity of car ECU and the need for security as it creates an ample amount of opportunities for hackers.
These ECUs for engine telemetry, brake, adaptive cruise control, park assist, etc. are connected wired or wirelessly to communicate with each other. They communicate with CANbus, MOST bus, or FlexRay networks. Threat models of automotive are based on real-world and theoretical attacks. Real-world attacks are associated with physical attributes of a car (steering, braking, parking, etc.) compromising passenger safety, while theoretical attacks are associated with hacking GPS data, radio signals, and multimedia systems compromising patient privacy.
Researchers demonstrated various vulnerabilities by remotely sending commands to the CANbus of a car and gaining control of infotainment systems (microphones, speakers, GPS, etc.) and telematics (fuel, engine, tire, etc.).
There are multiple hardware and software security measures that need to be implemented by the OEM of ECU in the manufacturing environment. Infineon AURIXTM 32-bit MCUs with embedded hardware security modules help architects to enable secure boot operations and secure storage of cryptographic keys for encrypted communication and secure OTA updates. Further CANbus is a broadcast network and an easy target for hackers to listen to the messages from the network and then perform DoS, sniffing, and spoofing attacks on the network. By using AURIXTM HSM, these CAN messages are encrypted, and in-vehicle networks are secured. Other mechanisms are certificate management, and public key infrastructure (PKI) based hardware root of trust to make ECU secure. OEMs need to create multiple sub-networks of ECU and restrict the remote access of critical ECUs.

Advanced Driver Assistance System (ADAS)
ADAS expose a large attack surface as it is the most important component in the connected car ecosystem. It has a direct impact on passenger safety and weakness in cybersecurity of ADAS will lead to fatal injury or death of the passenger.
ADAS and self-driving cars include various sensors like radar, LiDAR, ultrasonic, and camera which fusions the accurate 360-degree representation of surrounding of the car. Algorithms of camera image analysis, sensor fusion, video processing which are based on neural networks or deep learning systems are vulnerable to cyber-attacks.
Various vulnerabilities on ADAS have been demonstrated in multiple types of research. The Max-Planck Institute for Intelligent Systems and the University of Tübingen have demonstrated that small changes in the environment like small painting on a wall or stickers could cause malfunctioning of autonomous vehicle image analysis algorithm. The image analysis algorithm has vulnerability and it confused with the actual object and representation of object. Other researchers have demonstrated vulnerabilities of ADAS cameras with manipulating traffic signs, road markings, and speed limit signs.
To mitigate the threats on ADAS, sensor fusion and image analysis algorithms should be secured by periodically performing threat analysis and risk assessment on vulnerable assets. The interconnected RF communication channels used in ADAS network requires logical segregation. Vulnerability Assessment and Penetration Testing (VAPT) of all ADAS modules is required to perform to identify and remediate various threats on connected car ecosystem.
V2X Communication
V2X communication consists of the vehicle to everything communication, which incorporates vehicle-to-vehicle (V2V) and vehicle to infrastructure (V2I) communication. V2V is sensor data sharing between the cars for car distance, collision distance, and others. V2I communication is the exchange of data between roadside units for traffic management and emergency information to drivers.
V2X communication is a critical component for connected car ecosystem and compromise of this can lead to road fatalities. V2X infrastructure consists of an external interface which is equipped with various wireless technologies such as Bluetooth, BLE, ZigBee, Wi-Fi, LTE, 5G, etc. Hackers can easily target such communication channels and manipulate the data displayed to drivers with wrong traffic updates and inaccurate distances of the next car. It also sends inaccurate data to V2I and V2V networks causing collisions.
V2X communication requires secured messaging between different V2X elements. The communication needs to be encrypted and secured with Public Key Certificates using signed messages. This will authenticate the sender identity and only allow after authentication. To secure wireless communication, these signed messages need to be changed regularly and should have a shorter validity period.
Final Thoughts
Ponemon Institute study in 2019 by security professionals found that 30% of current companies are not having an established in-house product cybersecurity program or teams. With innovation in the autonomous cars industry and government regulations for security audits and frameworks requirement, the security of the connected car ecosystem is essential.
With our IoT security services span across the device, OS/firmware, application, and communication networks, we help automotive manufacturers in developing a robust connected car ecosystem. Our security services cater threat modelling, VAPT, security program design and implementation and improvement. Our automotive expertise across ADAS, Telematics, Connected Vehicles (V2X), and Infotainment & Clusters help global OEMs in introducing next-generation solutions. We have strong experience in automotive product engineering, AUTOSAR compliant ECU development, and HMI design with ISO26262 compliant functional safety.
Connect with our expert today to know more about our automotive services.