Introduction
Joint Test Action Group, commonly known as JTAG, is a widely used interface for testing and debugging electrical devices. It provides a standardized method for accessing and controlling internal components of integrated circuits (ICs). JTAG finds applications in various industries, including consumer electronics, aerospace, automotive, and telecommunications.
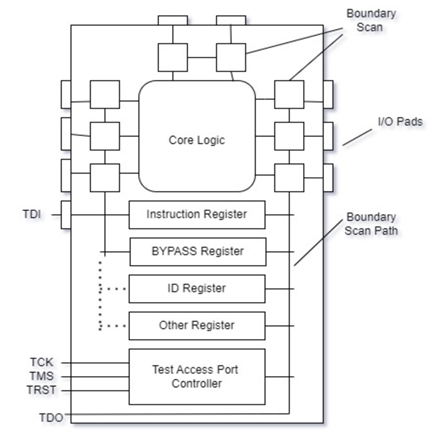
JTAG Architecture
The JTAG architecture comprises a Test Access Port (TAP), Instruction Register (IR), and Data Register (DR). The Test Access Port connects the JTAG controller and the test object. The Data Register facilitates data transmission between the device and the JTAG controller, while the Instruction Register stores and manages the instructions used to operate the device.
Fig-1 JTag Architecture
JTAG Operation Modes
JTAG supports four main operation modes: Select-DR/IR, Run-Test/Idle, Test Logic Reset, and Capture-DR/IR. These modes enable various operations, such as device resets, data input/output changes, and instruction register updates.
JTAG Applications
Debugging
Engineers utilize JTAG for checking and modifying internal registers, performing boundary scans, and monitoring device signals. This aids in identifying and resolving hardware issues, reducing development time and costs.
In-System Programming (ISP)
JTAG enables in-system programming, allowing changes to firmware or configuration data of programmable devices like microcontrollers and FPGAs without physically removing the chip from the circuit board.
Boundary Scan
JTAG’s boundary scan capability allows engineers to test individual components, verify interconnections, and detect manufacturing flaws in complex PCBs without the need for physical probes.
Chip Testing
JTAG is extensively used to thoroughly test integrated circuits during production, ensuring their quality and reliability before incorporation into finished goods.
Fig.2 Chip Testing
JTAG Tools and Ecosystem
There are many distinct JTAG tools and software pieces that aid various facets of JTAG-based development. Emulators, boundary scan testers, JTAG debuggers, and programming tools are some of these tools. Additionally, several computer languages and software frameworks support JTAG, making it easier for designers to incorporate JTAG features into their hardware creations.
Attacks Performed on JTAG
Despite being a useful tool for debugging and testing electrical equipment, JTAG (Joint Test Action Group) is not immune to security flaws. We’ll look at a few typical attacks that might jeopardize hardware security by targeting JTAG ports.
Physical Access Attacks
These attacks take place with direct physical access to the device’s JTAG interface. Attackers can exploit this access to carry out illegal actions, harvest private data, or introduce harmful codes. Typical physical access assaults against JTAG include:
Direct Probing: Attackers can directly interact with JTAG pins via connections or probes, circumventing any security precautions.
Chip-Off Attacks: If the JTAG interface cannot be accessed externally, attackers may remove the chip from the device and use other methods to gain access to the JTAG interface.
Side-Channel Attacks
Side-channel attacks exploit unintentional information leakage caused by physical characteristics like power usage, electromagnetic emissions, or timing variations during JTAG operations. These attacks can be categorized into the following:
Power Analysis: Attackers can gain insight into internal states and cryptographic keys used by the device by analyzing power consumption patterns during JTAG operations.
Timing Analysis: Attackers can deduce critical information, such as encryption keys or execution pathways, by analyzing the timing of JTAG signals.
Glitch Attacks
Glitch attacks target the precise timing or voltage levels of JTAG signals to make a device behave improperly. Attackers can disrupt regular JTAG processes, bypass security measures, or extract data by carefully injecting glitches. Types of glitch attacks include:
Voltage Glitching: Manipulating voltage levels during specific JTAG operations causes the device to behave incorrectly.
Clock Glitching: Altering the clock signal induces timing errors and exploit JTAG controller vulnerabilities.
Firmware Manipulation
Attackers may attempt to modify or replace the firmware currently running on the device using the JTAG interface. They can install malicious firmware, backdoors, or unauthorized programs through the JTAG port, potentially compromising or taking control of the device.
Mitigating JTAG Attacks
Attacks by JTAG (Joint Test Action Group) pose a serious risk to the hardware systems’ security. It is essential to put into practice efficient mitigation techniques in order to guarantee the integrity and confidentiality of sensitive information.
Secure JTAG Access
To avoid unauthorized manipulation, it’s crucial to restrict physical access to JTAG interfaces. Think about the following mitigating techniques:
Physical Protection: Secure JTAG connections should be placed in tamper-evident enclosures or regions with limited access as part of physical protection against physical assaults.
Access Controls: Implement robust authentication methods, such as passwords or biometric authentication, to limit access to JTAG interfaces to only authorized individuals.
Disable JTAG by Default
JTAG capability should be disabled by default in production systems or end-user devices to reduce the attack surface. This prevents the JTAG interface from being exploited unless it is expressly enabled for necessary testing or debugging.
Implement Secure JTAG Configurations
To lower the danger of unauthorized access, secure the JTAG controller and its configuration. Think about the following actions:
Password Protection: Require strong passwords in order to access the JTAG interface, making sure that initial setup changes the default passwords.
Encryption: Use encryption techniques to safeguard JTAG communications and stop eavesdropping and manipulation of JTAG processes.
Secure Boot and Firmware Validation
Use secure boot methods and firmware validation techniques to avoid unauthorised firmware alterations over the JTAG interface:
Secure Boot: During the boot process, check the integrity and authenticity of the firmware to make sure that only trusted and duly signed firmware is run.
Digital Signatures: Use cryptographic keys to sign firmware images, then check the signatures when the system boots to look for tampering or unauthorized changes.
Intrusion Detection and Monitoring
Implement monitoring and intrusion detection systems to identify possible JTAG assaults and take appropriate action. Think about the following actions:
Auditing and logging: Record JTAG operations and regularly check the logs for any unauthorized or suspicious access attempts.
Intrusion Detection Systems (IDS): Implement IDS tools that track JTAG communication and sound an alarm when suspicious or malicious behaviour is seen.
System Integrity Checks: Run routine hardware and firmware integrity checks to spot any alterations or tampering attempts.
Continuous Security Updates
Keep your hardware devices’ firmware up to date with the most recent security fixes. Patches are frequently released by manufacturers to fix identified flaws and enhance the overall security of their devices. To secure protection against new threats, quickly apply these updates.
eInfochips, a leading global provider of product engineering and semiconductor design services, has extensive cybersecurity capabilities to help organizations safeguard themselves from various types of attacks. By finding the weaknesses in their systems and lowering the potential of attacks, organizations may benefit from our services including Hardware Testing, Firmware Testing, Debugging, vulnerability assessment, and security audit. In order to comply with security industry standards, rules, and guidelines like those set forth by the National Institute of Standards and Technology (NIST), the European Network and Information Security Agency (ENISA), the Open Web Application Security Project (OWASP), the Massachusetts Institute of Technology Research and Engineering (MITRE), and the IoT Security Foundation, the company has also helped businesses develop, deploy, and manage security solutions on a global scale.